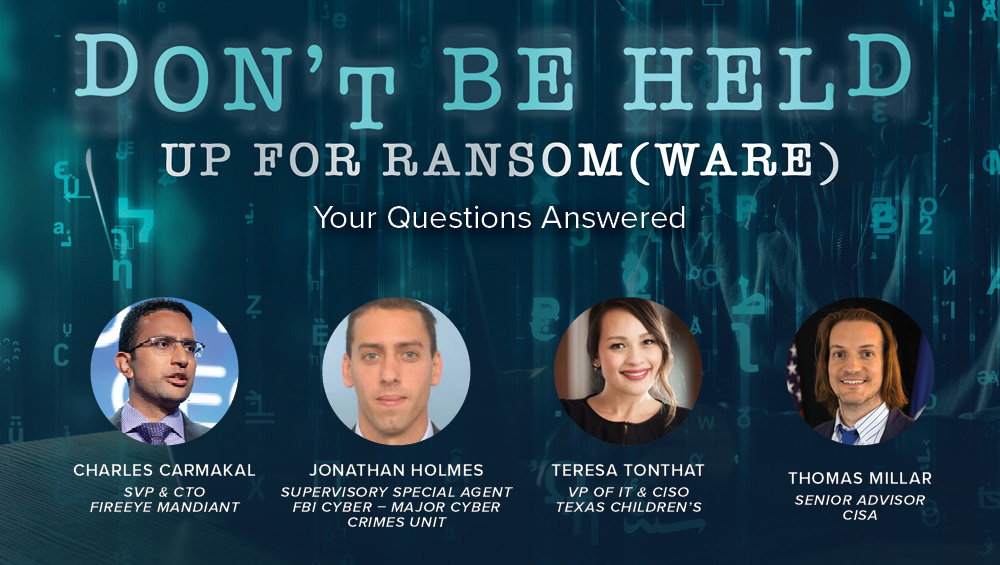
Charles Carmakal, SVP & CTO at FireEye Mandiant, Jonathan Holmes, Supervisory Special Agent at FBI Cyber – Major Cyber Crimes Unit, Teresa Tonthat, Vice President of IT & CISO at Texas Children’s, and Thomas Millar, Senior Advisor at Cybersecurity and Infrastructure Security Agency (CISA) collaborated to answer viewer questions from our latest webinar, “Don’t Be Held Up for Ransom(ware)”. If you missed this webinar or would like to watch it again, you can view it below.
What are one or two of the top strategies (at a high level), that organizations can implement to drastically lower their risk of a successful ransomware attack?
At a high level, organizations should do the following:
1. Reduce their attack surface (e.g. MFA on remote access, patch Internet-facing systems, and strong DMZ controls)
2. Minimize credential exposure when on systems (e.g. disabling wdigest, Protected Users Security Group)
3. Minimize lateral movement within the internal network.
More technical details can be found here.
What is the likelihood that bad actors will start to sell information about how to breach the victim companies, so that even if they don't do it again, someone else gets a head start on doing it?
It is possible that some actors will publicize details of how they breached organizations, likely to further embarrass victims. However, the same general approach is used to break into organizations over and over, so it's well documented.
At times it appears as though communication with the FBI is a one-way street where private organizations provide but we don’t get robust context or actionable information in return. I understand that a lot of this is due to confidentiality, but how can we make collaboration with the FBI more valuable bi-directionally to get ahead of these campaigns?
While organizations may not see immediate results, the FBI has had several positive outcomes with respect to indictments, arrests, and other actions that have helped organizations over the long term.
Charles, while I generally agree with your view on "Pay or not Pay," I still lean towards not paying. Why? Because I am not a believer in the trustworthiness of criminals. As you later mentioned, there will still be backdoors, they still have a copy of your data, and there is no guarantee that they will provide the decryption keys. What are your thoughts on this?
I agree, you can only trust threat actors so much. Before paying an actor, we look at historical track records with actors. Have they provided working decryption tools? Have they published data after being paid? Etc. You will also ask the threat actor for proof of working decryption tools (i.e. you provide them with a sample of encrypted data to decrypt) or a list of the files that were stolen. Those data points are considered as part of the payment evaluation process. And yes, I do agree that threat actors are criminals, and they can go back on their word at any time.
What should a company do when they realized they have no option but to pay the ransom? What’s the first step they should take, and can you name a few entities who they should reach out to first? How should they approach such entities (especially when there is no prior engagement)?
They should seek advice from the experts: legal, forensics, negotiator, and law enforcement. Let me know if you'd like specific recommendations of firms that can help.
What is the approximate frequency of Ransomware attacks?
We are aware of multiple intrusions almost every single day.
If you enjoyed this webinar, be sure to visit Second Thursdays for other great cybersecurity webinars.